With good reason, we at Logility have been consistently talking and writing about the urgent need for building resilient supply chains. Among the many harsh lessons taught by 2020, the importance of a durable, nimble, fault-tolerant supply chain was paramount. The supply shock that started in China in February, followed by the demand shock when the global economy shut down, exposed vulnerabilities in both the production plans and supply contingencies of businesses everywhere. Weaknesses became apparent with temporary trade restrictions and shortages of critical supplies in pharmaceuticals, medicine, and many other industries.
When it comes to ensuring, and better yet coordinating, consistency of supply sources and accuracy of demand sensing, supply chain professionals have made progress convincing stakeholders that a holistic approach to resilience is the right approach. (Indeed, much good work has come via the implementation of Integrated Business Planning.) If the importance of resilience gets diluted and filed under ‘IT project’ or ‘inventory reduction ideas,’ beware.
In the same way that planners have worked to demonstrate the broad and meaningful impact of initiatives to create healthier supply chains, it’s prudent – and timely – to expand the definition of resilience to include cybersecurity.
As evidence, Gartner recently published a report titled Ransomware is an Operational Problem. It summarizes a blog post by Barika Pace, a Gartner senior director and analyst specializing in securing emerging technologies, highlighting that responsibility for security goes beyond IT and risk leaders. If that doesn’t change, she points out, we may be stuck in a cycle of never-ending ransomware attacks followed by extortion.
If the discussion is exclusively with the CISO and the CIO working with risk and security operations, Barika suggests that you should double down on your cryptocurrency holdings because the “bad actors” may find an opportunity in your organization. There exists a growing security puzzle consisting of aging infrastructure, bad cyber hygiene, poor end-of-life equipment management, employee reluctance to work with cybersecurity staff, and increased use of original equipment manufacturer (OEM) devices and software providers. The proliferation of the Industrial Internet of Things (IIoT) and operational technology (OT) has expanded the use of OEM devices and the role third parties play in your security.
How Has COVID Changed the Game?
Ransomware is not new, but COVID-19 gave attackers a new advantage in two ways:
- Working From Home (WFH). Gartner calls it ‘bad cyber hygiene’. Before COVID, 17 percent of U.S. employees worked from home five days or more per week, a share that increased to 44 percent during the pandemic. However, not enough has been invested in understanding WFH connections, access needs and data path weaknesses and risks.
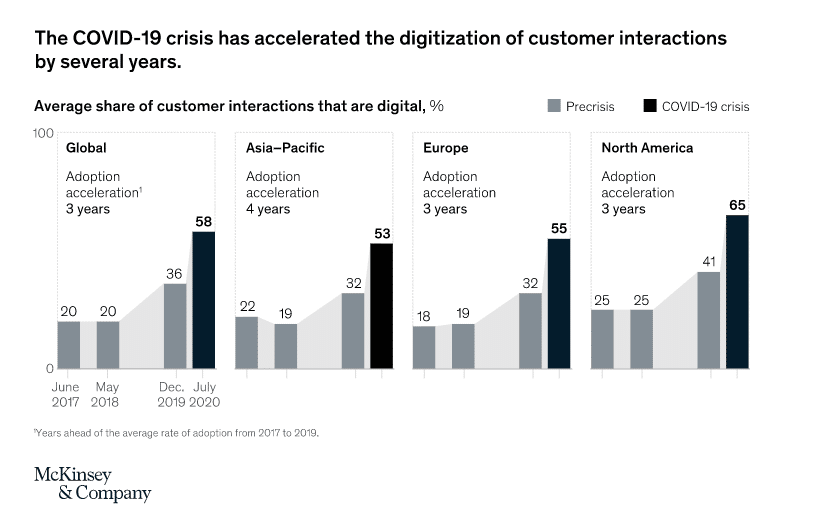
- Accelerated digitization. According to McKinsey & Company, overall adoption of digital technologies had sped up by three to seven years in a span of months. New survey results show that this acceleration is also happening at the level of core business practices; what was considered best-in-class speed for most business practices in 2018 is now slower than average.
In short, corporations forced employees to go home and customers to go digital, and to do both very quickly. Cyber-criminals took notice and took advantage. In this new environment, speed is only advantageous if the delivered product is secure.
Logility Enhances Customer Experiences with Microsoft Azure
At Logility, we consider ourselves your trusted innovation partner in a broad sense, which includes doing our part to ensure your operating environment is secure from “chip to cloud.” To that end, we’ve partnered with Microsoft to make our comprehensive suite of solutions available through Microsoft Azure. Azure strengthens Logility’s ability to provide a high-performing, secure and reliable environment.
The statistics are impressive. Microsoft invests over a billion dollars annually into cybersecurity and has 3,500 dedicated cybersecurity professionals working in hundreds of data centers in 50 global regions. Because security is in an ever-evolving state, the size of the threat is both large and constantly changing. Microsoft leverages collective intelligence to keep pace with threats. The Microsoft Intelligence Security Graph brings together signals from many Microsoft products at massive scale, including data from 450 billion authentications per month across one billion devices.
The rationale for the partnership is simple: it allows us to focus on building core value, which in turn helps our customers do the same.
Read more about Logility’s partnership with Microsoft Azure here.

Written by
Donald L. Thomas
Chief Information Officer
Short bio
Donald L. Thomas, Chief Information Officer, has more than 40 years of experience in development, implementation and support of supply chain solutions and is known for his ability to simplify and resolve technical challenges while positioning customers for success with the company’s software solutions. Having joined the company in its infancy, Mr. Thomas held several key positions within American Software, including vice president of manufacturing systems, and then led the Logility startup as it transitioned to client/server and now web-based solutions. Mr. Thomas holds a Bachelor of Industrial Engineering degree from Auburn University.